[NEBULA] I need separate lan for every port of the NSG50 (or NSG100)
 Ally Member
Ally Member



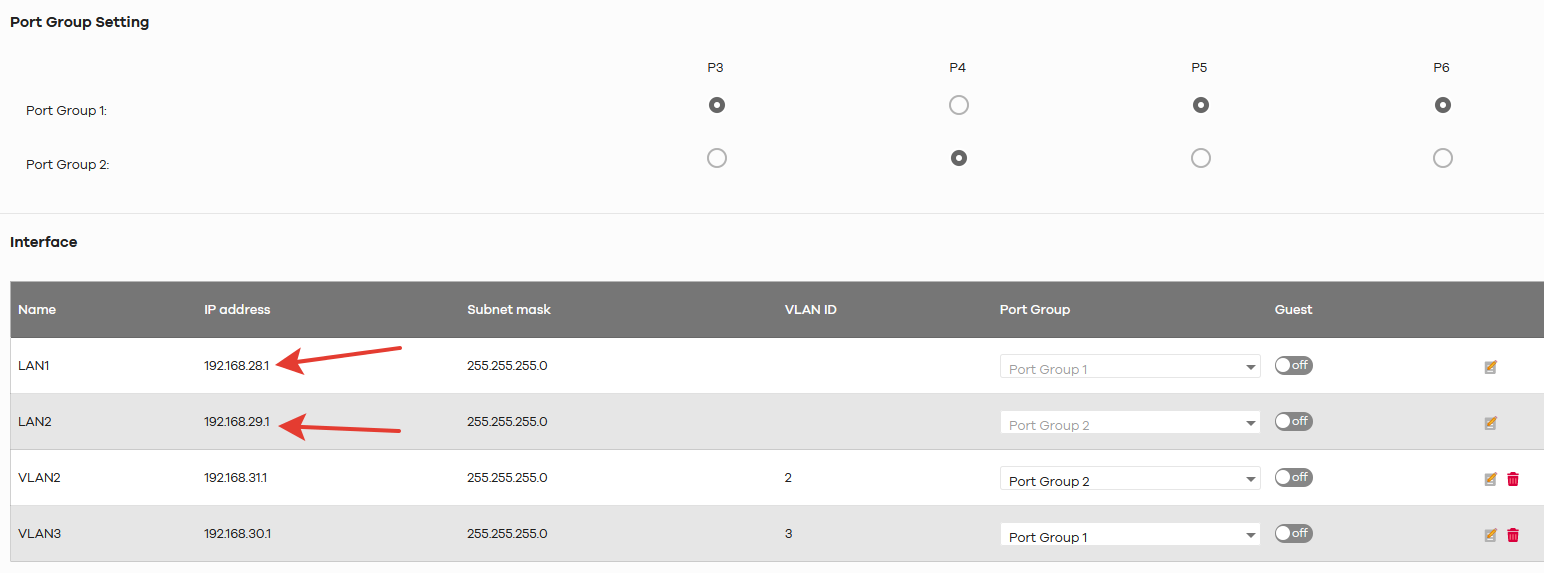
I can configure two subnets with help of the port groups
but I need ti separate every port to its own subnet.
I don't know how to do this.
I think that VLAN can help me, but I don't clearly understand how to stick VLAN to Port
All Replies
-
Hi @progreccor ,
Welcome to Zyxel Community!!
Yes, VLAN could help to separate every subnet.
But I would like to clarify if your goal is to create different subnet and all of these subnets don't have the ability to communicate to each other? If yes, you will need to create a firewall rule to block the communication for every VLAN.
Sincerely yours,
Jonas,
Jonas,0 -
But how could I link VLAN to each psychical port on NSG?
(suppose I don't have switch yet)
I can link VLAN only to two port groups but I have four physical ports
0 -
Hi @progreccor ,
Due to product level definition NSG50, NSG100 & NSG200 was designed with two port groups which means only two LAN ports, for a normal usage, creating a VLAN virtual interface and connecting a switch could achieve the goal, because basically connecting only 4 end devices like PC to NSG is comparatively uncommon.
The second option is, if there is no budget concern, purchasing NSG300 could also be the solution as it supports 6 individual LAN ports.
Note: Maximum VLAN interface for NSG50 is 8 and 16 for NSG100. Please refer to the attached for detailed information.
Sincerely yours,
Jonas
Jonas,0 -
I have got to say, this limitation is a step back for ZyXEL. Previous devices allowed for creation of discreet LANs for each LAN interface on a box. You also allowed for users to rename these interfaces. Why has ZyXEL degraded these capabilities?
0 -
Appreciate for the comments. Generally, for the current design, two port groups could already fulfill application requirements and you may also create a virtual interface. May I know if it is convenient to share your real application.
Thanks,
Jonas
Jonas,0 -
For the common use it is very inconvenient that device have only two port groups.
Let us suppose that I want to use common switches (like ZYXEL ES-105AV3) to connect to every physical port.
And I can't create LAN for every physical port - only two!
That is sad...
0 -
What kind of scenario do you have that every physical port must provide a different network?
If the switches are not able to handle VLAN, I guess you don't need them, so you could just use one LAN and set all ports to that LAN. Or use the two LANs and allocate them in 2/2 ports.If you need to block something, you could use firewall rules.
"You will never walk along"0 -
Suppose I have four floors or simply four offices...
And I need different LAN for every. And I don't need more complicated switches - ZYXEL ES-105AV3 enough.
So If I buy this router without GS1920 or something like that - I can't get four different LANs with different IPs.
Why not? If I buy simple Keenetic router or D-LInk or others - I can do that scenario.
But with Zyxel - I can't!
And this is not obvious for buyers!
0 -
Will you need to isolate the LANs from each other or what's the main reason you need different networks?
There's always a way! I guess you use DHCP, so you can bind the devices MAC address to a certain range of IP address of the same LAN, based on to which port the devices are connected. Then you only need to block those ranges in the firewall rule...Might not work for your scenario but maybe you can share more precise details ?.
I get your point about the limitation, but to be honest I would rather rely on a switch to do this kind of segmentation through VLANS, leaving the security to the firewall. Just my personal opinion
"You will never walk along"1
Categories
- All Categories
- 390 Beta Program
- 2.1K Nebula
- 116 Nebula Ideas
- 78 Nebula Status and Incidents
- 5.1K Security
- 51 USG FLEX H Series
- 247 Security Ideas
- 1.3K Switch
- 69 Switch Ideas
- 914 WirelessLAN
- 34 WLAN Ideas
- 5.9K Consumer Product
- 211 Service & License
- 332 News and Release
- 71 Security Advisories
- 21 Education Center
- 5 [Campaign] Zyxel Network Detective
- 1.9K FAQ
- 879 Nebula FAQ
- 414 Security FAQ
- 220 Switch FAQ
- 194 WirelessLAN FAQ
- 46 Consumer Product FAQ
- 137 Service & License FAQ
- 34 Documents
- 34 Nebula Monthly Express
- 72 About Community
- 61 Security Highlight
 Zyxel Employee
Zyxel Employee

 Freshman Member
Freshman Member

