How to configure ACL to block unwanted traffic
 Zyxel Employee
Zyxel Employee



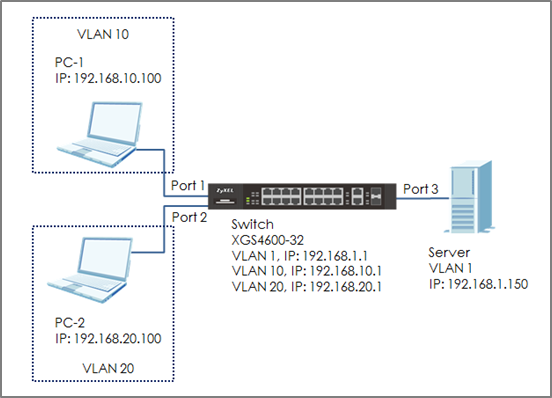
The example shows administrators how to use ACL to block unwanted traffic. We can set different criteria to identify unwanted traffic. The example will use ACL to prevent only a single host in VLAN 10 from accessing the Server.
Note:
All network IP addresses and subnet masks are used as examples in this article. Please replace them with your actual network IP addresses and subnet masks. This example was tested using XGS4600-32.
1. Configure VLAN and Route Traffic
1-1. Configure the VLAN setting (VLAN 10 and VLAN 20) on Switch.
1-2. Configure the VLAN IP interfaces on Switch.
2. Configure the Classifier
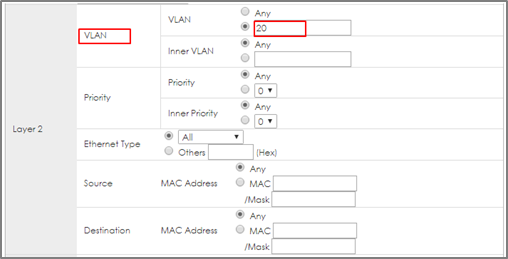
2-1. Set up the Classifier: Go to Menu > Advanced Application > Classifier > Classifier Configuration. Set up Classifier: For VLAN 20.
2-2. The Classifier of VLAN 20: Check the “Active” box and key in the classifier Name. Set Layer 2 > VLAN as 20 and Layer 3 > Destination as 192.168.1.150/32. Press “Add”.
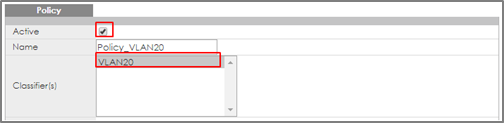
3. Configure the Policy Rule
3-1. Set up the Policy Rule: Go to Menu > Advanced Application > Policy Rule. The policy rule of VLAN 20: Check the “Active” and key in the Policy Rule Name. Select the Classifier in VLAN 20 (VLAN20). Set up the action to do if match this Classifier: Action > Forwarding > Discard the packet. Press “Add”.
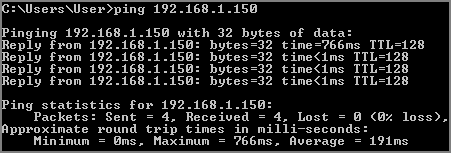
4. Test the Result
4-1. PC-1 can ping Server successfully.
4-2. Due to the ACL setting, the PC-2 (VLAN 20) cannot ping Server successfully.
5. What Could Go Wrong
5-1. When setting up the Classifier, remember to consider both source and destination. In the example, if we only created a policy rule for source VLAN 20, but didn’t create the policy rule for destination IP (Server IP: 192.168.1.150), the switch will block all the traffic from VLAN 20 no matter where the destination is.
5-2. Go to Menu > Advanced Application > Classifier. Check “Count”. If the traffic matches the classifier, the Match Count for this classifier should be increasing every time the web page refreshes.
Categories
- All Categories
- 383 Beta Program
- 2.1K Nebula
- 116 Nebula Ideas
- 80 Nebula Status and Incidents
- 5.1K Security
- 76 USG FLEX H Series
- 247 Security Ideas
- 1.3K Switch
- 69 Switch Ideas
- 907 WirelessLAN
- 34 WLAN Ideas
- 5.9K Consumer Product
- 209 Service & License
- 335 News and Release
- 71 Security Advisories
- 21 Education Center
- 5 [Campaign] Zyxel Network Detective
- 1.9K FAQ
- 890 Nebula FAQ
- 415 Security FAQ
- 233 Switch FAQ
- 203 WirelessLAN FAQ
- 46 Consumer Product FAQ
- 137 Service & License FAQ
- 34 Documents
- 34 Nebula Monthly Express
- 73 About Community
- 62 Security Highlight